Security has been at the forefront of digital transformation. It is vital for your business that your applications and infrastructure environments be protected against possible threats. Opcito's end-to-end cloud security and monitoring services detect and neutralize security breaches and threats.
We use the latest security and monitoring solutions to provide 24x7 automated threat monitoring and detection. Our systems monitor and detect misconfigurations across your cloud infrastructure, network, and applications in real-time to flag vulnerabilities and save you from costly breaches.
We ensure minimized risk with security compliance measures for your hybrid and multi-cloud environments. Gain control and fortify your cloud systems with heightened monitoring and security measures with our certified team of security experts.
Opcito’s team of experienced and certified experts specialize in monitoring of the cloud environment to keep it safe and always up & running. Our strong policies and security guidelines ensure threat-free operations and in case of breach a threat is detected and prevented well in advance to save additional losses.
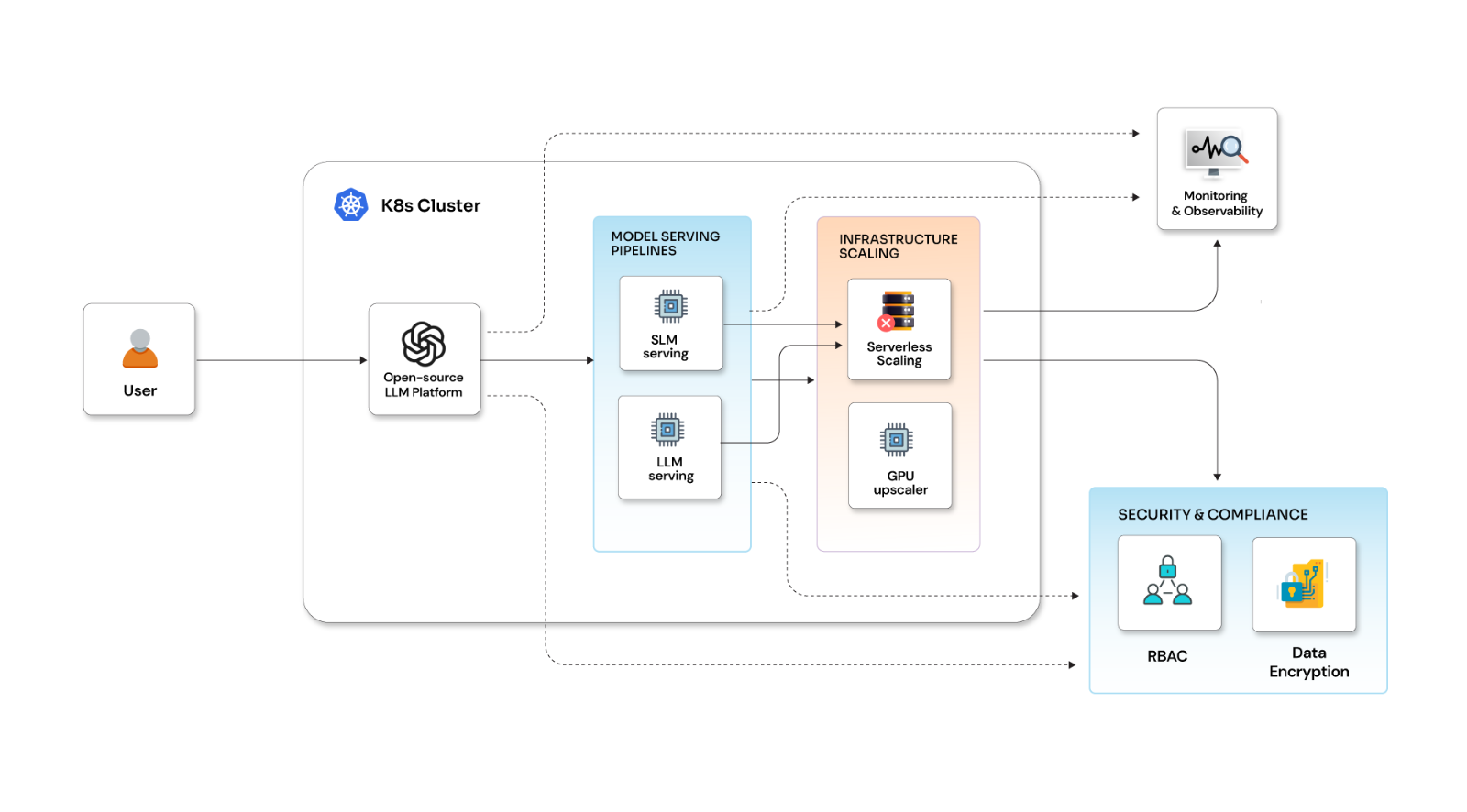
With our automated monitoring systems, we use metrics to measure performance and ensure system health is always optimal. We have expertise in security monitoring in AWS, security monitoring in Azure, and security monitoring on Kubernetes.
Use metrics to ensure application performance is optimal and you get the expected level of service. We pinpoint issues with the application in real-time and rectify any errors that occur.
Monitoring of your virtual and hybrid cloud environment vitals across distributed locations to help identify problems before they become issues to reduce downtime and fix shortcomings.
Cloud sprawl or overprovisioning of cloud servers can eat up resources. Proper monitoring, clubbed with robust procedures and policies help in using services optimally to promote overall cost reduction.
Ensure uninterrupted service delivery using continuous performance monitoring of cloud databases with key performance indicators to ensure admins have deep visibility of the database performance at any time.
A strong policy structure regarding safe user practices, training of users in security aspects and protocols, and other best practices, along with the use of effective tools, can help prevent, detect, and mitigate threats.
The health of the cloud infrastructure is paramount. We are always on our toes, ensuring your systems are up to date. Opcito's regular maintenance activities help maintain the overall health of the cloud infrastructure and systems, with our team of experts providing support to solve any technical challenges.
and monitoring services

We use access control, authentication, and authorization with the right framework of policies and tools combined with passwords and multi-factor authentication to ensure that only the right people have access to your applications and data.
We assess the integrated security measures in your cloud setup using customized security assessment frameworks. Based on the analysis, we recommend a course of action to tighten the security of your cloud infrastructure, data, and applications.

With the advancement in container space and integrations with cloud, image signing has become a vital part of security. We ensure the security of cloud and container environments with the master encryption key Image for signing images before moving them to containers, ensuring their authenticity.

Effective disaster recovery measures in case of data loss are central to business continuity planning. Regular backups, validity testing of backups, and tools to ensure continuous operations and business continuity.

Opcito's disaster management and automated recovery services help you continue your business without worrying about any mishaps. We manage disasters by providing flexibility and reliable failover for required services in case of service interruptions.

Prioritized security and the need to keep malicious attacks at bay need a well-maintained SBOM. We ensure enhanced visibility of the software supply chain and adhere to recent government and organizational standards for maintaining an SBOM.